Muddled Libra Shifts Focus to SaaS and Cloud for Extortion and Data Theft Attacks
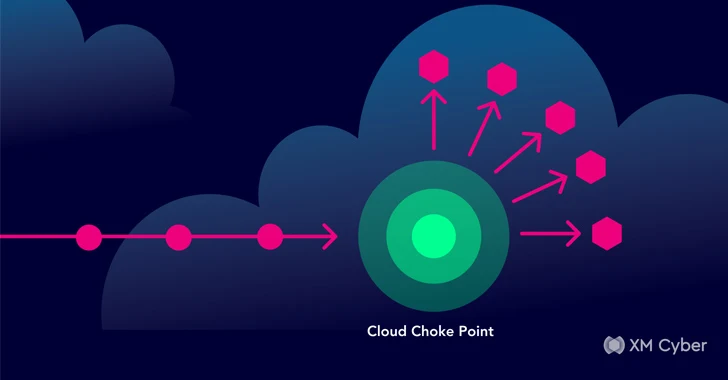
[ad_1] Apr 15, 2024NewsroomCloud Security /SaaS Security The threat actor known as Muddled Libra has been observed actively targeting software-as-a-service (SaaS) applications and cloud service provider (CSP) environments in a bid to exfiltrate sensitive data. “Organizations often store a variety of data in SaaS applications and use services from CSPs,” Palo Alto Networks Unit 42…